FAQ
Network Taps
Q: What is a Passive Network Tap?
+
Q: What is an Active Network Tap?
+
Q: Is there such a device as a truly passive Copper Gigabit Network Tap?
+
Q: If I deploy my monitoring device using a network tap, will my monitoring device be visible on the network?
+
Q: Are the power supplies on the taps hot swappable?
+
Q: If the tap is not set to autonegotiate in the firmware, is there still a delay on power off and back on?
+
Q: What is the “TCP Reset” or Traffic Injection feature in a tap and how is it used?
+
Q: Why isn't there a truly passive network tap offered that allows bi-directional traffic or traffic injection?
+
Q: What is auto-negotiation / speed sensing?
+
Q: What is a "Potential Point of Failure" and why should it be considered as part of any network access design that includes taps?
+
Q: If I deploy my monitoring device using a network tap, will my monitoring device be visible on the network?
+
Q: Are the taps equipped with redundant, load sharing power supplies?
+
Q: I want to install a large number of taps in a single rack but may have issues with the number of AC outlets required – how is this issue resolved?
+
SINGLEstream™ Link Aggregation Taps
Q: What is an Aggregation Tap?
+
Q: Why not just use a regular full duplex tap?
+
Q: Is there a tap that can provide both aggregated and non-aggregated output?
+
Q: Why do Datacom’s link aggregation capable taps have more than one output (monitor port)?
+
Q: Where would I use an aggregation tap in my network?
+
Q: Can I connect the output of a link aggregation tap to a matrix switch?
+
Q: Do aggregation taps forward VLAN tags through to the Monitoring tools?
+
Q: How does a link aggregation tap handle Layer 1 and Layer 2 traffic, and how does it affect security and network analysis?
+
VERSAstream™ Network Packet Broker
Q: What is a VERSAstream™ Network Packet Broker?
+
Q: Is the VERSAstream™ Network Packet Broker an out of band or an in-line device?
+
Q: Can the VERSAstream™ ports be inputs or outputs?
+
Q: Does the VERSAstream™ add latency to data copies going to my analytic tools?
+
Q: Where would I use the VERSAstream™ Network Packet Broker or Network Monitoring Switch?
+
Q: Does the VERSAstream™ support multiple speed inputs?
+
Q: What if my network or existing monitoring tools are not the same media type?
+
Q: What about aggregation and utilization rates?
+
Q: Are large buffer memories the right solution for oversubscription?
+
Q: What tools will work with the VERSAstream™ ?
+
Q: How can VERSAstream™ allow network management and security personnel to view data from a packet as it travels across the network?
+
Cables
Q: What cables are included with my purchase?
+
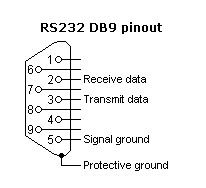
Q: What is the Pinout for the DB9 Serial ports on the SINGLEstream and VERSAstream products?
+
Q: For serial control of my 2x16SP-1000BT or 4x16SY-BT, what is the maximum length my control cable can be?
+
Q: What cables are needed to attach a Datacom Systems 2x16SP-1000BT, 4x16SY-BT and 4x16SY-SX to the network?
+